- Home
- »
- Network Security
- »
-
Industrial Control Systems Security Market Size Report, 2030GVR Report cover
![Industrial Control Systems Security Market Size, Share & Trends Report]()
Industrial Control Systems Security Market Size, Share & Trends Analysis Report By Component, By Solutions, By Services, By Security Type, By End-use, By Region And Segment Forecasts, 2024 - 2030
- Report ID: GVR-4-68040-167-5
- Number of Pages: 120
- Format: Electronic (PDF)
- Historical Range: 2018 - 2022
- Industry: Technology
Market Size & Trends
The global industrial control systems security market size was valued at USD 18.99 billion in 2023 and is projected to grow at a compound annual growth rate (CAGR) of 8.2% from 2024 to 2030. The increasing number of cyberattacks on critical infrastructure is the primary factor driving the growth of the industrial control systems security market. Furthermore, the growing adoption of big data analytics in ICS would support the market's overall expansion. Moreover, the strict government regulations related to customer identification program (CIP) serve to encourage the adoption of ICS security solutions. Additionally, rising industrial automation and virtualization also contribute to the expansion of the industrial control systems security market.
Various governments develop laws and policies to optimize cybersecurity standards for critical infrastructure protection. For instance, in September 2023, the Cybersecurity & Infrastructure Security Agency (CISA), a government agency for cybersecurity, released four industrial control systems advisories. For technical information and mitigations, CISA advises administrators and users to review the most recent ICS advisories that have been released. These advisories offer up-to-date information on ICS-related security vulnerabilities, threats, and issues. The industrial control systems (ICS) security market is anticipated to grow as a result of these government initiatives.
Organizations worldwide have their industrial control systems (ICS) exposed to the public internet. Threat advisories can take over physical infrastructure, such as water systems, traffic light systems, power grids, security systems, and more, if they are used maliciously. An attack of this magnitude might jeopardize national security, pose a serious threat to human safety, compromise data, and intellectual property, and seriously disrupt business. Therefore, Various organizations use security measures like firewalls to prevent unauthorized users from accessing their industrial control systems security.
The industrial control systems (ICS) security market is expanding due to rising investments in industrial control structures and digital technologies to meet the expanding demand for industrial control structures safety products and services. Various business sectors are experiencing global changes as a result of the developing technology landscape. As a result, industrial control systems and digital technology have combined to create a single environment. This greatly expands the possibilities for IoT and machine-to-machine (M2M) communication. As a result, the adoption of digital technologies causes industrial control systems to evolve into a collection of objects that interact with a system or with one another while being situated in a heterogeneous environment.
Market Concentration & Characteristics
The market growth stage is moderate, and the pace of the market growth is accelerating. Various sectors such as manufacturing, energy, oil and gas, metals and mining, healthcare, and transportation systems are increasingly adopting IOT-based solutions. The advancement and transition of industrial control automation and robotics technology are primarily attributable to control systems.
Furthermore, government initiatives like France's Plan Industrial and Germany's Industry 4.0 have a significant impact on the demand for IoT solutions and are expected to drive the industrial control systems security market.
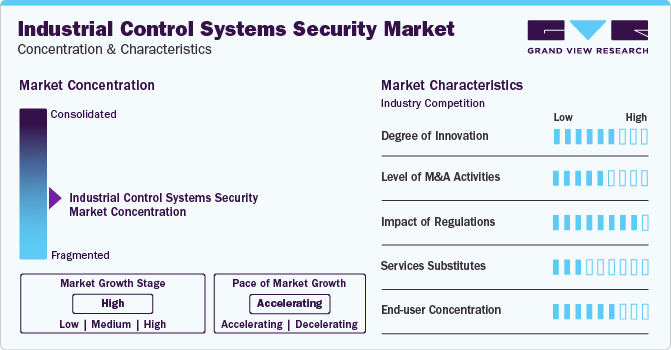
High-profile cyberattack campaigns including Black Energy and Havex has explained that traditional tools can be insufficient in preventing these highly advanced intrusions. Thus, the convergence of OT and IT in cyber-physical ecosystems demand for technology that can analyse that how both these OT and IT systems interact.
End-user concentration can be termed as a critical driving factor in the ICS market. As energy, utilities, shipping, manufacturing, and other forms of heavy industry are witnessing a rise in convergence of OT and IT owing to the growth of industrial internet of things (IIoT), it is now becoming a critical challenge providing easy access to pivot in organizational networks and devices. Thus, the demand of advanced ICS security solutions is constantly growing among various end-user industries.
End-use Insights
The energy and utilities segment held the largest market share in 2023. Energy and utilities organizations need secure identities for business processes. By implementing ICS software solutions, energy and utility organizations enable strong authentication to utility processes and enforce IAM for OT and IT. Market players offer full transparency and control over access, and end users need to provide suppliers and partners for remote services. Thus, the ICS solution consists of a detailed audit trail with ease of use. Thus, driving the market growth of the segment.
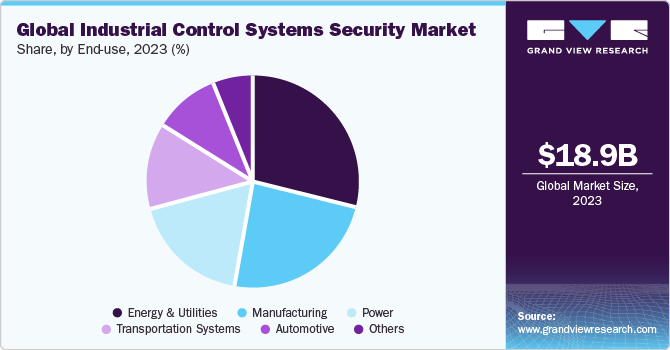
The automotive segment is expected to hold the highest CAGR through 2030. Automation in the automotive industry is becoming more common due to the growing cost of labor and the intense pressure automotive manufacturers face to meet deadlines. Using devices like industrial personal computers (PCs), programmable logic controllers (PLCs), and programmable automation controllers (PACs), automation solutions automate industrial processes without requiring human interaction. Automation could increase productivity worldwide. In addition, since a large portion of work in automotive professions can be automated, some of these occupations may be partially automated. Thus, driving the market growth of the segment.
Regional Insights
North America held the highest market share of more than 33% in 2023. North America is anticipated to hold the largest market share for the ICS security market over the forecast period. The demand for security solutions is rising due to the increasing use of connected devices and the internet of Things in a range of local businesses. Additionally, it is anticipated that the number of security solution providers in the U.S. will increase in the forecasted period. Therefore, the segment is expected to grow significantly in the forecasted period.

Asia Pacific's industrial control systems security market is expected to register the fastest growth over the forecast period. Several companies are introducing advanced technologies in countries such as China with significant potential in terms of technology adoption, digitization, and government support to boost yearly outputs. For instance, in order to maximize its production capacity and reach an annual output of 50,00 tonnes of rolled copper strip and foil production, Northern Copper Industry Co. Ltd, a company based in China, producer of raw material copper stock, selected ABB to implement an automation and electrical system that included an ABB Ability System 800xA distributed control system (DCS). Therefore, it is driving the market growth in the region.
Component Insights
The solution segment accounted for the largest revenue share in 2023, contributing more than 70.3% of the overall revenue. With the proactive approach provided by the ICS security solution, business environments can reduce risk, threats can be blocked before they affect critical assets, and industrial operations can be seamlessly improved. Furthermore, The ICS security solution delivers integrated AI security, threat prevention, secure 5G connectivity, and more to protect ICS for energy and utilities, manufacturing, and transportation sectors. Thus, these factors collectively drive the industrial control systems (ICS) security solution market growth.
The services segment is expected to register considerable growth with a CAGR of more than 8.6% over the forecast period. ICS security services include IT/OT managed security services, ICS security risk assessments, and ICS security management programs. ICS Security Integration Services minimize the total cost of ownership (TCO) for continuing ICS security management, lower the risk of disruption from cyberattacks, and offer constant visibility into threats and vulnerabilities to the ICS environment. Industrial control system security services, which combine advisory, system integration, and managed services in the field of ICS security, can assist a range of industries in lowering disruption risks, minimizing operational downtime brought on by cyberattacks, and enhancing the robustness of industrial systems and networks. Thus, the factors above collectively drive the industrial control systems (ICS) security market’s growth.
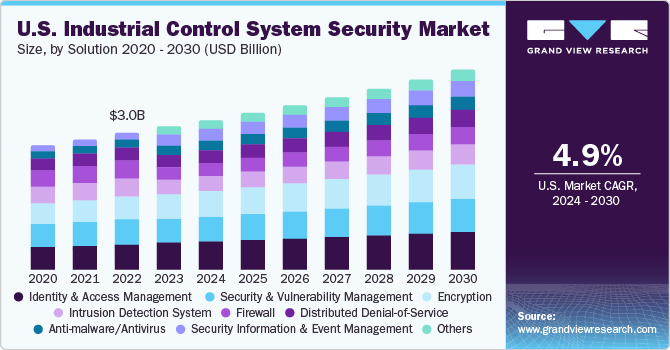
Solution Insights
The Identity and Access Management (IAM) segment accounted for the largest revenue share in 2023. Various factors, such as an increase in security breaches and an increase in identity-related fraud, have contributed to the IAM market's growth. Furthermore, more qualified cybersecurity specialists within businesses could be needed to ensure market expansion. The introduction of AI/ML-powered services, growing SMEs' adoption of IAM, and scalability benefits are also driving the market's growth. These elements offer organizations proactive security measures and improved identity management capabilities, which contribute to the market's promising growth potential. Consequently, driving the growth of the IAM segment in the forecasted period.
The encryption segment is expected to exhibit the highest growth rate of CAGR over the forecast period.Encryption solution helps in protecting industrial data, network, and devices by encoding data in a way that it can only be decoded and decrypted by an individual that holds the correct encryption code. Encryption is an application of cryptographic technologies, which is are also used to assist other critical security functions, including message integrity, authentication, and non-repudiation. Thus, the uses of cryptology can be considered as significantly important in the ICS environment helps in simplifying encryption and managing ICS traffic.
Services Insights
The professional services segment accounted for the largest revenue share in 2023. Professional services plans and programs for industrial control systems security to be customized to the unique needs and features of ICS environments and technologies. The ICS should also be integrated with and consistent with current IT security programs, practices, and experience. Organizations periodically update and review their ICS security programs and plans to take into account modifications to standards, laws, technologies, operations, and facilities' unique security requirements. One of the main objectives of industrial organizations is to secure and protect their assets. Thus, OT and IOT security specialists support ICS security professional services, providing technical expertise as well as a comprehensive understanding of compliance frameworks.
The managed services segment is expected to exhibit the growth rate of CAGR over the forecast period. Managed services for industrial control systems assist businesses with maintaining an accurate asset inventory, managing vulnerabilities and patches, maintaining network device uptime and configuration, managing backups and restorations, maintaining application allow listing, and deploying new devices with the proper configuration. Thus, the industrial control systems security managed services are expected to be driven by the aforementioned factors.
Security Type Insights
The network security segment held the largest market share in 2023. IoT and smart devices are revolutionizing industrial control system (ICS) networks, boosting productivity, efficiency, and usability in ICS networks, they also impact ICS security in significant ways.Due to the infrequency of device changes connected to them, ICS networks are rather static. These networks are observed to create a baseline, after which any anomalies or newly connected devices are identified, and an alert is sent out regarding them. Thus, the network security segment is expected to grow significantly in the forecasted period.
The end point is expected to hold the highest CAGR through 2030. Organizations can secure their network and the entry points that connect internal data by using endpoint security solutions. Organizations use advanced security solutions as their first line of defense in cybersecurity to protect their enterprise network infrastructure. End-user companies use artificial intelligence (AI)-based solutions to protect their business units from outside threats and data breaches. Additionally, in order to provide better endpoint protection, it is now imperative that technologies such as cloud services and IoT be used more frequently. Al-enabled security solutions are available from companies such as Cisco Systems, Inc., Palo Alto Networks, FireEye, and others to identify endpoint attacks. Thus, the segment is expected to grow significantly in the forecasted period.
Key Companies & Market Share Insights
Some of the key players operating in the market include Microsoft Corporation; IBM Corporation, ABB Group; and Schneider Electric
-
Microsoft Corporation offers complete ICS and operational technology (OT) security solutions that’s helps in providing enhanced visibility across all IoT and IT assets, along with this the company’s ICS solution helps companies in accelerate the incident response with a comprehensive and unified view of the entire cybersecurity posture, including IT network, business-critical networks, and OT environments.
-
IBM Corporation offers comprehensive ICS solutions that Connecting industrial systems to an IT network that offers industrial environments a more wholistic view of entire industrial ecosystems and individual equipment along with operating and operating these systems in a more effective and efficient manner.
-
Yokogawa Electric Corporation, DarkTrace, Nozomi Networks are some of the emerging market participants in the industrial control system (ICS) security market.
-
Yokogawa Electric Corporation offers a wide range of industrial automation and test and measurement solutions. By integrating superior technology with project management, engineering services, and maintenance, the company delivers field proven operational safety, efficiency, quality, and reliability.
-
Darktrace’s utilizes advanced AI technology that monitor, track, and analyze every detail of industrial environment, delivering continuous insights, and offering early warnings of compromise across the entire industrial system.
Key Industrial Control Systems Security Companies:
- ABB Group
- BAE Systems
- Cisco Systems
- Check Point
- DarkTrace
- Fortinet
- Honeywell International Inc.
- IBM Corporation
- Kaspersky Labs
- Microsoft Corporation
- Nozomi Networks
- Palo Alto
- Siemens AG
- Trend Micro Incorporated
- Yokogawa Electric Corporation
Recent Developments
-
In January 2023, Yokogawa Electric Corporation, an electrical engineering, and software company, partnered with McAfee Corporation, an antivirus software company, to offer comprehensive and enhanced IT security solutions for the field of industrial automation. The partnership would address the critical threat of digital threats to industrial control systems by leveraging McAfee Corporation's cyber security expertise and Yokogawa's proven global track record of delivering control system solutions.
-
In October 2022, Valmet, a global technology solution and service provider announced a strategic partnership with TXOne Networks, that offers CS and industrial IoT (IIoT) security solutions. Valmet aims at integrating TXOne Networks’s solutions for endpoint protection, security inspection, and network defenses with the leading Valmet’s Industrial internet and automation solutions, which is expected to strengthen the ability of industrial customers to better understand, protect, respond, and recover from a cyberthreats by effectively utilizing Valmet’s Cybersecurity Services.
-
In December 2023, IBM Corporation announced collaboration with Palo Alto Networks to strengthen the client’s end-to-end postures and navigate the security threats. The major focus of the partnership will focus on two key areas which includes securing the cloud transformations and modernizing the security operations.
Industrial Control Systems Security Market Report Scope
Report Attribute
Details
Market size value in 2024
USD 20.51 billion
Revenue forecast in 2030
USD 32.88 billion
Growth rate
CAGR of 8.2% from 2024 to 2030
Base year for estimation
2023
Historical data
2018 - 2022
Forecast period
2024 - 2030
Quantitative units
Revenue in USD billion and CAGR from 2024 to 2030
Report coverage
Revenue forecast, company market share, competitive landscape, growth factors, and trends
Segments covered
Component, solutions, services, security type, end-use, region
Regional scope
North America, Europe, Asia Pacific, Latin America, MEA
Country scope
U.S.; Canada; Germany; UK; Spain; France; Italy; Japan; China; India; South Korea; Australia; Brazil; Mexico; Argentina; South Africa; UAE; Saudi Arabia
Key companies profiled
ABB Group; BAE Systems; Cisco Systems; Check Point; DarkTrace; Fortinet; Honeywell International Inc.; IBM Corporation; Kaspersky Labs; Microsoft Corporation; Nozomi Networks; Palo Alto; Siemens AG; Trend Micro Incorporated; and Yokogawa Electric Corporation.
Customization scope
Free report customization (equivalent up to 8 analysts working days) with purchase. Addition or alteration to country, regional & segment scope.
Pricing and purchase options
Avail customized purchase options to meet your exact research needs. Explore purchase options
Global Industrial Control Systems Security Market Report Segmentation
The report forecasts revenue growth at the global, regional, and country levels and provides an analysis of the latest trends in each of the sub-segments from 2018 - 2030. For the purpose of this study, Grand View Research has segmented the industrial control systems security market report on the basis of component, solutions, services, security type, end use, and region.
-
Component Outlook (Revenue; USD Billion; 2018 - 2030)
-
Solution
-
Services
-
-
Solutions Outlook (Revenue; USD Billion; 2018 - 2030)
-
Anti-malware/Antivirus
-
Firewall
-
Encryption
-
Identity and Access Management (IAM)
-
Security and Vulnerability Management
-
Security Information and Event Management (SIEM)
-
Distributed Denial-of-Service (DDoS)
-
Intrusion detection systems (IDS)/Intrusion Prevention System (IPS)
-
Others
-
-
Services Outlook (Revenue; USD Billion; 2018 - 2030)
-
Professional Services
-
Managed Services
-
-
Type Outlook (Revenue; USD Billion; 2018 - 2030)
-
Endpoint
-
Application
-
Network
-
Database
-
-
End Use Outlook (Revenue; USD Billion; 2018 - 2030)
-
Energy & Utilities
-
Manufacturing
-
Power
-
Transportation Systems
-
Automotive
-
Others
-
-
Regional Outlook (Revenue; USD Billion; 2018 - 2030)
-
North America
-
U.S.
-
Canada
-
-
Europe
-
U.K.
-
Germany
-
France
-
Italy
-
Spain
-
-
Asia Pacific
-
China
-
India
-
Japan
-
Australia
-
South Korea
-
-
Latin America
-
Brazil
-
Mexico
-
Argentina
-
-
Middle East & Africa (MEA)
-
UAE
-
Saudi Arabia
-
South Africa
-
-
Frequently Asked Questions About This Report
b. The global industrial control systems security market size was estimated at USD 18.99 billion in 2023 and is expected to reach USD 20.51 billion in 2024.
b. Global industrial control systems security is expected to grow at a compound annual growth rate of 8.2% from 2024 to 2030 to reach USD 32.88 billion by 2030.
b. The solution segment accounted for the largest revenue share in 2023, contributing more than 70.3% of the overall revenue. With the proactive approach provided by the ICS security solution, business environments can reduce risk, threats can be blocked before they affect critical assets, and industrial operations can be seamlessly improved.
b. ABB Group; BAE Systems; Cisco Systems; Check Point; DarkTrace; Fortinet; Honeywell International Inc.; IBM Corporation; Kaspersky Labs; Microsoft Corporation; Nozomi Networks; Palo Alto; Siemens AG; Trend Micro Incorporated; and Yokogawa Electric Corporation.
b. The increasing number of cyberattacks on critical infrastructure is the primary factor driving the growth of the industrial control systems security market. Furthermore, the growing adoption of big data analytics in ICS would support the market's overall expansion.
Share this report with your colleague or friend.
![gvr icn]()
NEED A CUSTOM REPORT?
We can customize every report - free of charge - including purchasing stand-alone sections or country-level reports, as well as offer affordable discounts for start-ups & universities. Contact us now
![Certified Icon]()
We are GDPR and CCPA compliant! Your transaction & personal information is safe and secure. For more details, please read our privacy policy.
We are committed towards customer satisfaction, and quality service.
"The quality of research they have done for us has been excellent."