- Home
- »
- Network Security
- »
-
Privileged Access Management Market Size & Share ReportGVR Report cover
![Privileged Access Management Market Size, Share & Trends Report]()
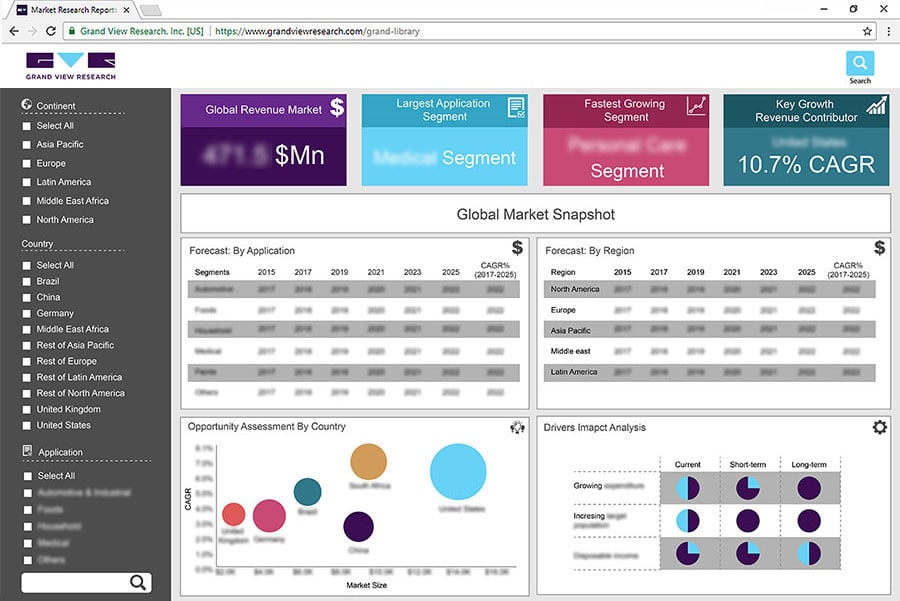
Privileged Access Management Market (2023 To 2030) Size, Share & Trends Analysis Report By Type (Software, Services), By Application (Small & Medium-sized Enterprises, Large Enterprises) By End Use, By Region, And Segment Forecasts
- Report ID: GVR454741
- Number of Report Pages: 0
- Format: PDF
- Historical Data: ---
- Forecast Period: 1 - 2030
- Industry: Technology
- Report Summary
- Table of Contents
- Segmentation
- Methodology
- Download FREE Sample
-
Download Sample Report
The privileged access management (PAM) market is related to the provision of security solutions for companies to protect their digital assets from being accessed by unauthorized or malicious users. PAM tools help companies manage and monitor privileged accounts, which are accounts with access to sensitive information or systems. With PAM solutions, companies can ensure that only authorized users have access to their valuable digital assets, which reduces the risk of security breaches or cyber-attacks. For instance, CyberArk, a company that helps protect organizations from cyberattacks, opened a new office in Hyderabad, India in March 2023. This office will be used for the research and development of new strategies and solutions to help keep people's online identities safe. They will also have a special team that helps with marketing and customer support. This new office will help CyberArk better serve its customers and partners in India.
Privileged Access Management is a fast-growing market because of various factors, including the requirement by organizations to improve their level of security as cyber threats and attacks become more advanced and frequent. PAM solutions give extra security by regulating and tracking access to essential systems and data. Strong legal requirements for protecting sensitive data exist in several areas, including healthcare and banking. By giving control over sensitive information, PAM systems help organizations in meeting these criteria. There is an increasing need for PAM solutions to manage privileged access in a cloud environment as more businesses shift their infrastructure to the cloud. Cloud infrastructure is unsafe for cyber-attacks, which can result in data breaches and other security incidents.
The COVID-19 pandemic has caused more people to work from home and use digital tools, which has increased the risk of cyber-attacks. To protect against these attacks, there has been an increasing demand for PAM solutions. These solutions ensure that only authorized people can access important digital information. Because of the pandemic, more businesses are using cloud-based PAM services as a cost-effective security solution.
Privileged Access Management Market Segmentation
-
By Solution Type
-
Privileged Access Management Software
-
Services
-
-
By Application
-
Small and Medium-sized Enterprises
-
Large Enterprises
-
-
By End Use
-
IT & Telecom
-
Healthcare
-
Energy & utility
-
Retail
-
Manufacturing
-
Government & Defense
-
Others
-
-
By Region
-
North America
-
U.S.
-
Canada
-
-
Europe
-
UK
-
Germany
-
France
-
Italy
-
Spain
-
Denmark
-
Sweden
-
Norway
-
-
Asia Pacific
-
Japan
-
China
-
India
-
Australia
-
Thailand
-
South Korea
-
-
Latin America
-
Brazil
-
Mexico
-
Argentina
-
-
Middle East & Africa
-
South Africa
-
Saudi Arabia
-
UAE
-
Kuwait
-
-
-
Key Players
-
CyberArk Software Ltd.
-
One Identity LLC
-
BeyondTrust Corporation
-
IBM Corporation
-
Zoho Corporation Pvt Ltd.
-
SecureAuth Corporation
-
Ekran System
-
HashiCorp
-
About the authors:
Author: GVR Network Security Research Team | Last Updated:
Share this report with your colleague or friend.
Need a Tailored Report?
Customize this report to your needs — add regions, segments, or data points, with 20% free customization.

ISO 9001:2015 & 27001:2022 Certified
We are GDPR and CCPA compliant! Your transaction & personal information is safe and secure. For more details, please read our privacy policy.