Market Segmentation
- Automated Breach and Attack Simulation Offering Outlook (Revenue, USD Million, 2018 - 2030)
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Automated Breach and Attack Simulation Deployment Mode Outlook (Revenue, USD Million, 2018 - 2030)
- Cloud
- On-premises
- Automated Breach and Attack Simulation Application Outlook (Revenue, USD Million, 2018 - 2030)
- Configuration Management
- Patch Management
- Threat Management
- Others
- Automated Breach and Attack Simulation End User Outlook (Revenue, USD Million, 2018 - 2030)
- Enterprises and Data Centers
- Managed Service Providers
- Automated Breach and Attack Simulation Regional Outlook (Revenue, USD Million, 2018 - 2030)
- North America
- North America Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- North America Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- North America Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- North America Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- U.S.
- U.S. Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- U.S. Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- U.S. Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- U.S. Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Canada
- Canada Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Canada Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Canada Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Canada Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Mexico
- Mexico Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Mexico Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Mexico Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Mexico Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Europe
- Europe Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Europe Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Europe Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Europe Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- UK
- UK Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- UK Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- UK Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- UK Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Germany
- Germany Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Germany Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Germany Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Germany Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- France
- France Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- France Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- France Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- France Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Asia Pacific
- Asia Pacific Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Asia Pacific Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Asia Pacific Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Asia Pacific Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- China
- China Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- China Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- China Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- China Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- India
- India Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- India Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- India Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- India Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Japan
- Japan Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Japan Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Japan Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Japan Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Australia
- Australia Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Australia Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Australia Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Australia Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- South Korea
- South Korea Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- South Korea Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- South Korea Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- South Korea Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Latin America
- Latin America Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Latin America Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Latin America Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Latin America Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Brazil
- Brazil Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Brazil Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Brazil Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Brazil Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Middle East & Africa
- Middle East & Africa Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Middle East & Africa Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Middle East & Africa Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Middle East & Africa Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- South Africa
- South Africa Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- South Africa Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- South Africa Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- South Africa Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- UAE
- UAE Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- UAE Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- UAE Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- UAE Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
- Saudi Arabia
- Saudi Arabia Automated Breach and Attack Simulation, By Offering
- Platforms and Tools
- Services
- Training
- On-demand Analyst
- Others
- Saudi Arabia Automated Breach and Attack Simulation, by Deployment Mode
- Cloud
- On-premises
- Saudi Arabia Automated Breach and Attack Simulation, by Application
- Configuration Management
- Patch Management
- Threat Management
- Others
- Saudi Arabia Automated Breach and Attack Simulation, by End User
- Enterprises and Data Centers
- Managed Service Providers
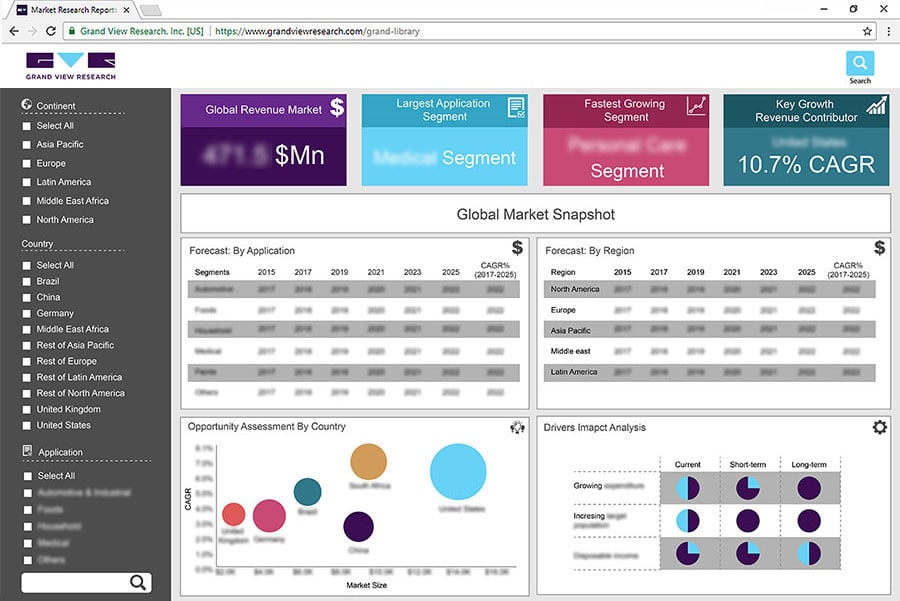
Report content
Qualitative Analysis
- Industry overview
- Industry trends
- Market drivers and restraints
- Market size
- Growth prospects
- Porter’s analysis
- PESTEL analysis
- Key market opportunities prioritized
- Competitive landscape
- Company overview
- Financial performance
- Product benchmarking
- Latest strategic developments
Quantitative Analysis
- Market size, estimates, and forecast from 2018 to 2030
- Market estimates and forecast for product segments up to 2030
- Regional market size and forecast for product segments up to 2030
- Market estimates and forecast for application segments up to 2030
- Regional market size and forecast for application segments up to 2030
- Company financial performance
We are committed towards customer satisfaction, and quality service.
"The quality of research they have done for us has been excellent."
Brian Moore, VP, NICCA USA, Inc.
testimonialsMore