- Home
- »
- Next Generation Technologies
- »
-
Zero Trust Security Market Size, Share & Trends Report 2030GVR Report cover
![Zero Trust Security Market Size, Share & Trends Report]()
Zero Trust Security Market Size, Share & Trends Analysis Report By Deployment (Cloud, On-premises), By Security Type (Network, Endpoint), By Authentication, By Organization Size, By Application, By Region, And Segment Forecasts, 2023 - 2030
- Report ID: GVR-4-68038-292-1
- Number of Report Pages: 154
- Format: PDF, Horizon Databook
- Historical Range: 2018 - 2021
- Forecast Period: 2023 - 2030
- Industry: Technology
Zero Trust Security Market Size & Trends
The global zero trust security market size was estimated to be USD 24.84 billion in 2022 and is anticipated to grow at a compound annual growth rate (CAGR) of 16.6% from 2023 to 2030. The growth of the zero trust security industry can be attributed to various factors, such as the growing trend in CYOD and BYOD concepts, increasing the number of cyber attacks, and improving regulation concerning cybersecurity, among others. The popularity of Bring Your Own Device (BYOD) and Choose Your Own Device (CYOD) trends is increasing significantly across organizations. Major Advantage, such as cost reduction on the endpoint infrastructure procurement front, has been driving the growth of zero-trust security. Moreover, the improvements in employee productivity ensured by allowing them to work on familiar devices drive the popularity of such concepts. The BYOD concept attained a reputation during the COVID-19 pandemic as organizations embraced the remote working model.
However, the BYOD and CYOD models allow employees to access business information and cloud applications using their dedicated endpoints, increasing the chances of data theft. Traditional cyber security measures fall short of preventing all forms of malware attacks or Advanced Persistent Threats (APT). Moreover, sophisticated cyber threat actors continuously monitor ways to penetrate through company networks, making it necessary for organizations to strengthen their cyber security infrastructure with zero trust methodologies. Zero trust methodologies help enterprises authenticate endpoints, users, and locations, allowing only trusted users to access organizational data. This can enhance the security of organizations that adopt the BYOD model.
The risk of cyberthreat is increasing considerably as cyber threat actors continue to explore vulnerabilities within an organization's IT infrastructure. Cyber threat actors gain access to critical information through vulnerabilities while maintaining anonymity. Cyber threat actors launch attacks such as persistent campaigns, advanced malware, spear-phishing, and watering holes to exploit organizational growth. For instance, according to research by Check Point Software Technologies Ltd., global cyberattacks increased by 28% in the third quarter of 2022 compared to 2021. Globally, the average number of weekly attacks per organization exceeded 1,100.
Over the years, targeted attacks on organizations across the globe have increased significantly. Attackers infiltrate a target organization's network infrastructure through endpoints, cloud-based applications, and other vulnerable networks. Such targeted attacks negatively impact a business's critical operations, leading to financial losses, loss of sensitive customer information, and loss of intellectual property. According to a sponsored study conducted by Trend Micro Incorporated with Quocirca, the most common objective of a targeted cyberattack is to impact organizational financial gains. Thus, a proactive detection layer is paramount to prevent the risk of losing regulated personal data, intellectual property, and financial loss. Through zero security principles, proactive detection and mitigation of cyber threats can be achieved by identifying the behavior of users infiltrating any network.
Security Type Insights
The endpoint security segment of the market by security type is projected to occupy the largest share, holding over 25% in 2022. The growth of the endpoint segment can be attributed to its benefits which include improved patch management, preventing insider threats, filtering content web, reducing AI threats, and streamlining cybersecurity, among others. Moreover, the companies in the market have been developing an enhanced solution to get better traction. The companies are involved in various strategic initiatives, including partnerships,s acquisitions, and mergers. For instance,e in January 2023, Xcitium cybersecurity provider announced a partnership with Carrier SI, a communication solution provider. The partnership is aimed at offering enhanced and affordable endpoint security. Moreover, the Carrier SI customers will now have access to the endpoint cybersecurity technology capable of containing known and unknown cyberattacks.
By security type, the network security segment is projected to have the highest growth from 2023 to 2030. The growth of the network security segment can be attributed to the benefits that network security offers, including mitigating risks, protecting proprietary information, and enabling a modern workplace, among others. Moreover, the development of 5G technology has also resulted in increased activities in the network security market by various companies. For instance, in January 2023, Trend Micro Incorporated announced a new subsidiary for “CTOne,” offering 5G network end-to-end security solutions. CTOne will be able to strengthen the digital resilience of vertical application fields and offer security for landing applications in a private 5G network environment.
Deployment Insights
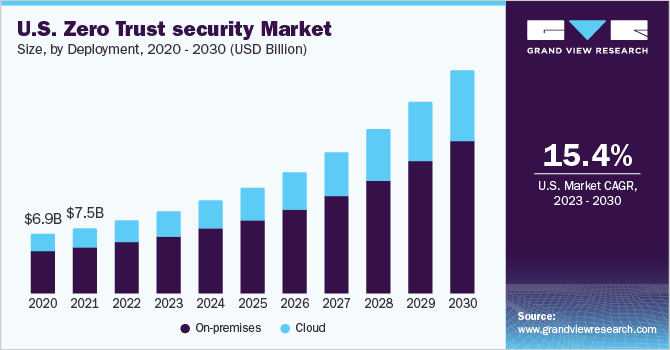
By deployment, the cloud segment of the market is projected to witness the highest growth rate of more than 17% over 2023-2030. The growth of the cloud-based segment can be attributed to the comfort and convenience the cloud-based deployment offers, which include the lesser need for in-house resources, less need for upfront costs, continuous monitoring, flexible options, automatic backups, and effective patch management, among others. The flexibility and scalability of the cloud-based deployment have been among the major factors that contributed to the growth of the cloud-based deployment of the market over 2023-2030.
The on-premises deployment segment held the largest revenue share of more than 77% in 2022 and is also projected to register a significant CAGR from 2023 to 2030 due to a high preference for this type of deployment. Organizations prefer to keep confidential data in-house rather than turning it over to a cloud provider. Moreover, on-premises solutions allow hands-on ownership and control of security monitoring, which offers a flexible and adaptive security program. This is expected to increase the demand for on-premises deployment over the forecast period. However, enterprises are migrating from on-premises to cloud-based solutions due to cost-effectiveness benefits.
Organization Size Insights
The large enterprise segment accounted for the maximum revenue share of over 76% in 2022 The segment will possess the predominant position throughout 2023-2030, owing to complex networking, programs, and endpoints of large-scale companies that need robust solutions to safeguard data by continuously validating and recording authentication in real-time. Companies rely on only adhering to compliance and entrusting authorized users with a higher risk of an internal breach. The compliant network does not guarantee a secured environment, as the threat to breach is not merely external but also could be by internal trusted sources. The zero-trust security model regards enterprise-authorized users with zero trust and provides the least privileged access to the users.
The small & medium enterprise segment is anticipated to register the fastest CAGR over the forecast period. The COVID-19 pandemic affected both large- and small-scale vendors as cases of data breaches increased while employees resorted to the remote working environment. Small- and medium-sized banking, financial institutions, IT, manufacturing, telecom, and retail companies are targeted as they need robust security solutions. Zero trust security ensures that the user with correct credentials is an internal and trusted user, not hackers relying on phishing and other methods to gain illegitimate access to login credentials. Thereby, the adoption of a zero-trust security model is increasing among SMEs for implementing multi-level authorization verification.
Authentication Insights
The multi-factor authentication segment led the market in 2022 with a revenue share of more than 75% and will expand at the fastest CAGR from 2023 to 2030. Multi-factor authentication was widely adopted across the industry due to the high level of security from multi-level authorization. The zero trust model’s key component in ensuring robust security is multi-factor authentication. It may be convenient for hackers to identify a single credential factor but multiple levels of verification and monitoring of access in real-time are vital in adhering to the zero-trust security model.
The method of single-factor authentication only verifies users with one credential, such as a password or OTP against the username. In such a mode of authentication, it is crucial to use a combination of letters, cases, numeric values, and symbols to ensure that a strong password is generated as it increases the complexity and time required by hackers to use permutation and combination for accessing the credential. However, the users often use simple credentials based on their personal identity information, such as date and year of birth or name, which reduces the security level. Hence, single-factor authentication is used in combination with other factors, which is driving the segment.
Application Insights
In 2022, the IT and telecom segment accounted for the highest revenue share of more than 45% and was projected to retain the leading position throughout the forecast period. Increased preference for cloud-based infrastructure and digital applications to procure information and facilitate business drives the need for unified, secure access and network solutions. In addition, the telecom industry incumbents primarily provide data transfer services and spend on several security-related technologies. With the increasing awareness about the benefits and applications of zero-trust security, the adoption of this model is expected to grow significantly.
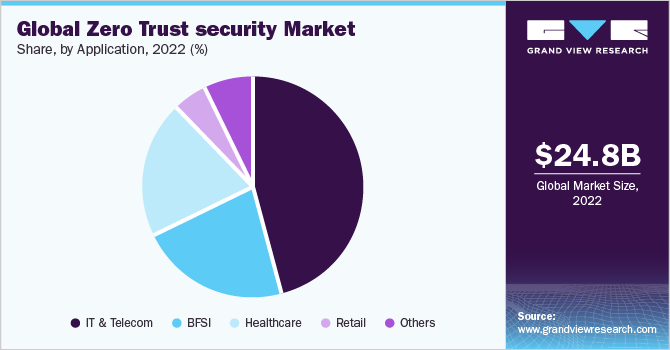
The healthcare segment is expected to register the fastest CAGR over the period 2023-2030. Continued innovation and implementation of technologies, such as telehealth services and analytics, to facilitate effective communication between end-users and entities are driving the need for secure network infrastructure services. Moreover, the increasing instances of cyber-attacks across healthcare IT infrastructures created the need for an advanced security framework for protecting critical information. These factors are expected to accelerate the demand for zero-trust security in the healthcare sector.
Regional Insights
North America dominated the global market in 2022 accounting for a revenue share of over 36% and is expected to register a significant CAGR from 2023 to 2030. The rising demand for solutions pertaining to the zero-trust security model due to the increasing security spending by the government and public authorities is expected to drive the regional market. Furthermore, the increased adoption of the Internet of Things (IoT), AI, and digital technology by SMEs and large enterprises and the increasing stringency in standards and policies for maintaining data privacy and security are contributing to regional market growth.

On the other hand, Asia Pacific is expected to exhibit the fastest CAGR from 2023 to 2030. The need to monitor the access to secure networks from unwarranted data breaches across public, financial, healthcare, and e-commerce enterprises is driving regional market growth. Multiple instances of data breaches and related consequences have increased the demand for threat-hunting services. For instance, in May 2020, two billion voters’ private data was made available for sale on the dark web, along with a threat to further sell the data of 200 billion voters.
Key Companies & Market Share Insights
The key players operating in the zero trust security market are broadening their product offerings, and are employing several inorganic growth tactics, such as mergers, partnerships, and acquisitions. For instance, in May 2021, Cisco Systems, Inc. acquired Slido, a polling and Q&A platform for virtual, live, and hybrid events and meetings. This acquisition will deliver key features and robust capabilities to the Webex experience. This acquisition also enables interaction with participants, making inclusive and effective decision-making. Prominent players dominating the global zero trust security market include:
-
Akamai Technologies
-
Appgate
-
Broadcom
-
Check Point Software Technologies Ltd.
-
Cisco Systems, Inc.
-
Cloudflare, Inc.
-
CrowdStrike
-
Forcepoint
-
Fortinet, Inc.
-
IBM
-
Musarubra US LLC
-
Microsoft
-
Okta
-
Palo Alto Networks
-
Zscaler, Inc.
Zero Trust Security Market Report Scope
Report Attribute
Details
Market size value in 2023
USD 28.14 billion
Revenue forecast in 2030
USD 82.45 billion
Growth Rate
CAGR of 16.6% from 2023 to 2030
Base year for estimation
2022
Historical data
2018 - 2021
Forecast period
2023 - 2030
Report updated
May 2023
Quantitative units
Revenue in USD Billion and CAGR from 2023 to 2030
Report coverage
Revenue forecast, company market share, competitive landscape, growth factors, and trends
Segments covered
Security type, deployment, organization size, authentication, application, region
Regional scope
North America; Europe; Asia Pacific; Latin America; and Middle East & Africa
Country scope
U.S.; Canada; Germany; UK; France; Italy; Spain; China; India; Japan; South Korea; Australia; Brazil; Mexico; Argentina; U.A.E.; Saudi Arabia; South Africa
Key companies profiled
Akamai Technologies; Appgate; Broadcom; Check Point Software Technologies Ltd.; Cisco Systems, Inc.; Cloudflare, Inc.; CrowdStrike; Forcepoint; Fortinet Inc., IBM; Musarubra US LLC; Microsoft; Okta; Palo Alto Networks; Zscaler, Inc.
Customization scope
Free report customization (equivalent up to 8 analysts working days) with purchase. Addition or alteration to country, regional & segment scope.
Pricing and purchase options
Avail customized purchase options to meet your exact research needs. Explore purchase options
Global Zero Trust Security Market Report Segmentation
This report forecasts revenue growth at regional and country levels and provides an analysis of the latest industry trends in each of the sub-segments from 2018 to 2030. For this study, Grand View Research has segmented the global zero trust security market based on security type, deployment, organization size, authentication, application, and region.
-
Security Type Outlook (Revenue, USD Billion, 2018 - 2030)
-
Network Security
-
Data Security
-
Endpoint Security
-
Cloud Security
-
Others
-
-
Deployment Outlook (Revenue, USD Billion, 2018 - 2030)
-
On-premises
-
Cloud
-
-
Organization Size Outlook (Revenue, USD Billion, 2018 - 2030)
-
SMEs
-
Large Enterprise
-
-
Authentication Outlook (Revenue, USD Billion, 2018 - 2030)
-
Single-factor authentication
-
Multi-factor authentication
-
-
Application Outlook (Revenue, USD Billion, 2018 - 2030)
-
IT & Telecom
-
BFSI
-
Healthcare
-
Retail
-
Others
-
-
Regional Outlook (Revenue, USD Billion, 2018 - 2030)
-
North America
-
U.S.
-
Canada
-
-
Europe
-
Germany
-
UK
-
France
-
Italy
-
Spain
-
-
Asia Pacific
-
China
-
India
-
Japan
-
South Korea
- Australia
-
-
Latin America
-
Brazil
-
Mexico
-
Argentina
-
-
Middle East & Africa
-
U.A.E
-
Saudi Arabia
-
South Africa
-
-
Frequently Asked Questions About This Report
b. The global zero-trust security market size was estimated at USD 24.84 billion in 2022 and is expected to reach USD 28.14 billion in 2023.
b. The global zero-trust security market is expected to grow at a compound annual growth rate of 16.6% from 2023 to 2030 to reach USD 82.45 billion by 2030.
b. North America emerged as a dominant regional zero-trust security market capturing 36.92% of the overall zero-trust security revenue share in 2022.
b. Some key players operating in the zero-trust security market include Akamai Technologies, Appgate, Broadcom, Check Point Software Technologies Ltd., Cisco Systems, Inc., Cloudflare, Inc., IBM, Microsoft, Okta, and Palo Alto Networks,
b. Key factors that are driving the zero-trust security market growth include the increase in cyber theft, internal data breach, and proliferation of endpoint devices coupled with the rising adoption of cloud technology.
Share this report with your colleague or friend.
![gvr icn]()
NEED A CUSTOM REPORT?
We can customize every report - free of charge - including purchasing stand-alone sections or country-level reports, as well as offer affordable discounts for start-ups & universities. Contact us now
![Certified Icon]()
We are GDPR and CCPA compliant! Your transaction & personal information is safe and secure. For more details, please read our privacy policy.
We are committed towards customer satisfaction, and quality service.
"The quality of research they have done for us has been excellent."