- Home
- »
- Next Generation Technologies
- »
-
Zero Trust Network Access Market, Industry Report, 2033GVR Report cover
![Zero Trust Network Access Market Size, Share & Trends Report]()
Zero Trust Network Access Market (2026 - 2033) Size, Share & Trends Analysis Report By Component (Solution, Services), By Deployment (Cloud, On-Premises, Hybrid), By Enterprise Size, By Application, By End Use (BFSI, Healthcare), And Segment Forecasts
- Report ID: GVR-4-68040-852-8
- Number of Report Pages: 120
- Format: PDF
- Historical Range: 2021 - 2025
- Forecast Period: 2026 - 2033
- Industry: Technology
- Report Summary
- Table of Contents
- Segmentation
- Methodology
- Download FREE Sample
-
Download Sample Report
Zero Trust Network Access Market Summary
The global zero trust network access market size was estimated at USD 1.97 billion in 2025 and is projected to reach USD 11.03 billion by 2033, growing at a CAGR of 24.2% from 2026 to 2033. The rapid migration of applications to cloud and SaaS environments is driving the market growth.
Key Market Trends & Insights
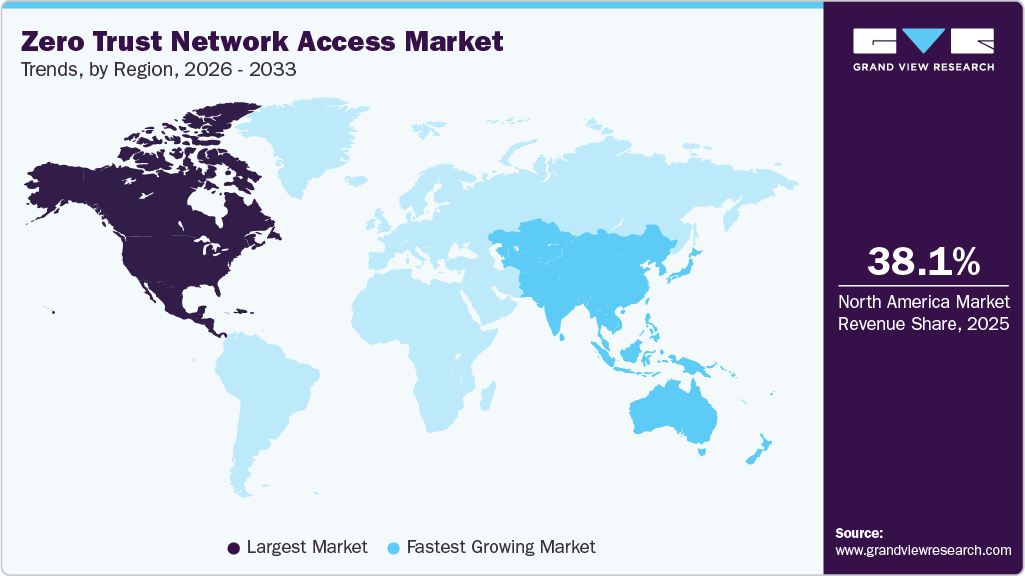
- North America held 38.1% revenue share of the global zero trust network access industry.
- In the U.S., rising frequency and sophistication of cyberattacks is accelerating the demand for zero trust network access systems.
- By component, the solution segment held the largest revenue share of over 68% in 2025.
- By deployment, the cloud segment held the largest revenue share in 2025.
- By enterprise size, the large enterprises segment held the largest revenue share in 2025.
Market Size & Forecast
- 2025 Market Size: USD 1.97 Billion
- 2033 Projected Market Size: USD 11.03 Billion
- CAGR (2026-2033): 24.2%
- North America: Largest market in 2025
- Asia Pacific: Fastest growing market
The growing emphasis on identity-centric security is fueling the zero trust network access (ZTNA) market growth. Identity has become the new security perimeter in modern IT environments. ZTNA solutions integrate closely with identity providers and authentication systems. They evaluate user identity, device health, and contextual factors before granting access. Continuous authentication reduces reliance on static credentials. Enterprises invest heavily in identity and access management initiatives. ZTNA complements these efforts by enforcing identity-based access at the application level. As identity-driven security strategies mature, ZTNA adoption increases. This alignment strengthens the market’s growth trajectory.Another important driver is the demand for improved user experience and simplified access management. Traditional VPNs often create performance bottlenecks and complex user workflows. ZTNA provides seamless access without requiring full network tunnels. Users connect directly to authorized applications with minimal latency. IT teams benefit from centralized policy management and reduced operational complexity. Simplified access improves productivity and reduces support costs. Organizations prioritize solutions that enhance both security and usability. ZTNA meets these dual objectives effectively. This user-centric advantage accelerates adoption across enterprises.

Regulatory compliance and data protection requirements also play a significant role in driving the zero-trust network access industry. Industries such as finance, healthcare, and government face strict access control and auditing requirements. ZTNA enables granular access policies and detailed activity logging. Continuous monitoring supports compliance with evolving regulations. Organizations can demonstrate control over who accesses sensitive data and applications. Regulatory pressure encourages the adoption of more robust access frameworks. Zero-trust architectures align well with compliance mandates. As regulations tighten, demand for ZTNA solutions grows.
Another driver is the increasing need to secure third-party and contractor access. Modern enterprises rely on external partners for development, maintenance, and operations. Granting network-level access to third parties introduces significant risk. ZTNA allows organizations to provide secure, limited access to specific applications. Third-party users are isolated from the broader network. Access can be easily provisioned and revoked. This reduces exposure and simplifies governance. As third-party collaboration increases, ZTNA becomes essential. This ecosystem complexity supports market expansion.
The convergence of ZTNA with broader secure access service edge strategies is also driving market growth. Organizations seek integrated security platforms rather than fragmented tools. ZTNA is a core component of unified security architectures. Integration with cloud security, web gateways, and endpoint protection enhances value. Unified platforms simplify deployment and policy management. Enterprises prefer scalable solutions that evolve with their needs. ZTNA’s role within integrated security frameworks strengthens its adoption. This architectural convergence reinforces long-term market momentum.
Component Insights
The solution segment dominated the zero trust network access market with a market share of 68.2% in 2025. The growing emphasis on identity-centric security models that prioritize least-privilege access and continuous authentication is driving segment growth. Organizations are recognizing that identity has become the new perimeter, particularly with the proliferation of remote work and third-party access. ZTNA solutions offer adaptive access control based on contextual factors, including user role, device posture, geographic location, and behavioral analytics. This shift reduces the risk of lateral movement within networks and mitigates insider threats by restricting access strictly to authorized applications rather than entire networks. Enterprises are also integrating ZTNA with identity and access management (IAM) systems to strengthen governance and auditability. As regulatory scrutiny around access controls increases, businesses are adopting comprehensive ZTNA solutions that support detailed logging, reporting, and compliance mapping. The ability of ZTNA platforms to enforce continuous verification instead of one-time authentication is accelerating their adoption across regulated industries.
The services segment is projected to be the fastest-growing segment from 2026 to 2033. The rising number and sophistication of cyberattacks targeting industrial infrastructure also amplify the demand for services. Attacks such as ransomware, phishing, and supply chain breaches can cripple production, endanger personnel, and disrupt national critical infrastructure. In response, companies are investing in services such as continuous monitoring, threat intelligence, and forensic analysis to enhance situational awareness and strengthen response capabilities. Managed Detection and Response (MDR) and Security Operations Center (SOC)-as-a-service offerings are gaining traction among industrial players who need around-the-clock security coverage but lack the internal resources to operate their SOCs.
Deployment Insights
The cloud segment dominated the market in 2025. The increasing focus on identity-centric security further drives cloud ZTNA adoption. Cloud-based ZTNA platforms integrate tightly with cloud identity providers and authentication services. Identity becomes the primary control point rather than the network location. Continuous verification ensures access decisions are context-aware. Cloud delivery supports real-time policy evaluation across environments. Organizations benefit from consistent identity enforcement for cloud and on-premise applications. This alignment strengthens the overall security posture. As identity-driven security strategies mature, demand for cloud ZTNA grows. This strategic alignment reinforces market growth.
The hybrid segment is projected to grow significantly from 2026 to 2033. The migration of mission-critical applications to hybrid environments is driving segment growth. Many organizations are reluctant to move all applications to the cloud due to latency, regulatory, or operational requirements. Instead, they adopt hybrid architectures where sensitive workloads remain on-premises while others transition to the cloud. Hybrid ZTNA enables secure access to this mix of legacy and modern applications without disrupting business continuity. It ensures that access controls can adapt to the specific security needs of each application type. This flexibility is crucial for regulated industries such as financial services, healthcare, and government, where certain data must remain on-site for compliance reasons.
Enterprise Size Insights
The large enterprises segment dominated the market in 2025. The push for digital transformation and modernization within large enterprises also significantly drives the ZTNA market. Digital transformation initiatives spanning customer experience platforms, IoT deployments, data analytics, and AI workloads require flexible, secure access to a wide range of resources. As large enterprises modernize legacy systems and launch new digital services, security must evolve in parallel. ZTNA supports this evolution by providing a security model compatible with agile development practices and continuous deployment pipelines. Rather than retrofitting legacy access controls, enterprises can embed zero trust principles into new digital products from the outset. This alignment between transformation initiatives and modern security frameworks positions ZTNA not just as a security solution but as a strategic enabler of digital business.
The small & medium enterprises (SMEs) segment is projected to be the fastest-growing segment from 2026 to 2033. The growing use of unmanaged and personal devices in SME environments is driving segment growth. Unlike large enterprises, SMEs often allow employees to use personal laptops, tablets, and mobile phones to access business applications due to cost constraints and the need for flexibility. This bring-your-own-device culture creates significant security challenges when using traditional access methods that assume trusted devices. Zero-trust network access evaluates device posture, security status, and contextual signals before granting access, even when the device is not fully managed. This capability is especially valuable for SMEs that cannot afford full device lifecycle management solutions. ZTNA allows them to enforce conditional access policies without requiring complete device ownership or control. This driver is reinforced as SMEs increasingly adopt mobile-first workflows and cloud-based productivity tools.
Application Insights
The application access control segment dominated the market in 2025. The growing prevalence of identity-based threats that specifically target application credentials rather than network infrastructure is a significant driver. Cyberattacks increasingly focus on stealing user identities, session tokens, and API keys to gain unauthorized access to applications. Traditional network security tools struggle to detect and prevent these attacks once credentials are compromised. Application access control within ZTNA frameworks continuously validates user identity, context, and behavior at the moment of application access. This allows organizations to enforce least-privilege principles dynamically rather than relying on static trust assumptions. By tying access decisions directly to identity and context, ZTNA reduces the effectiveness of credential-based attacks. Enterprises recognize that identity has become the new security perimeter, making application-level controls essential. This is especially important for applications that handle sensitive business, financial, or personal data.
The secure cloud connectivity segment is projected to be the fastest-growing segment from 2026 to 2033. The rising volume of east-west traffic between cloud workloads, users, and third-party services further drives segment adoption. Modern digital operations depend heavily on continuous data exchange across distributed cloud components. Securing this traffic at the network perimeter is ineffective because much of it never passes through traditional inspection points. Secure cloud connectivity under a ZTNA model enforces authentication and authorization at every access request. This reduces the risk of unauthorized lateral movement within cloud environments. Organizations increasingly recognize that internal cloud traffic must be treated as untrusted by default. ZTNA enforces this principle by continuously validating connections rather than assuming trust based on network location.
End Use Insights
The BFSI segment dominated the market in 2025. The rapid expansion of digital banking and financial services platforms is driving segment growth. Banks, insurers, and financial institutions are increasingly delivering services through mobile apps, web portals, and cloud-based platforms to meet evolving customer expectations. This digital expansion dramatically increases the number of access points to sensitive financial systems. Traditional perimeter-based security models are inadequate for protecting such highly distributed environments. Zero-trust network access enforces strict identity verification before granting access to any application, regardless of user location. BFSI organizations view this model as essential for securing online transactions and customer data. The ability to continuously validate users and devices aligns with the sector’s risk-averse culture. As digital financial services continue to grow, ZTNA adoption in BFSI accelerates as a core security enabler.

The IT & telecommunication segment is projected to be the fastest-growing segment from 2026 to 2033. The ongoing surge in cybersecurity threats and data breaches, which underscores the limitations of legacy security frameworks, is propelling the growth of the ZTNA market. As threat actors employ increasingly sophisticated tactics such as advanced persistent threats (APTs), ransomware, and credential stuffing attacks, organizations are discovering that traditional perimeter defenses leave them vulnerable to lateral movement once an attacker gains initial access. Zero trust approaches explicitly address this vulnerability by segmenting access to applications and data, reducing the blast radius of a compromise, and limiting an attacker’s ability to move freely within the environment. This continuous verification model means that every access request is scrutinized based on a variety of factors, including user identity, device health, location, and behavior patterns, making it significantly harder for unauthorized actors to exploit weak or stolen credentials. The high-profile breaches affecting enterprises, governments, and critical infrastructure have heightened board-level awareness of cybersecurity risks, prompting increased investment in next-generation security architectures like ZTNA.
Regional Insights
North America Zero Trust Network Access Market Trends
North America zero trust network access industry dominated the global market with a share of 38.1% in 2025. The need to reduce operational complexity and total cost of ownership influences the ZTNA market in North America, especially as enterprises seek to optimize their security investments. Traditional remote access solutions such as hardware-based VPNs often require substantial infrastructure, manual configuration, and significant maintenance overhead, which can strain IT and security teams. These approaches also tend to create fragmented security stacks, complicating policy management and slowing incident response. Zero-trust solutions, particularly those delivered through cloud-native or hybrid models, offer centralized policy management, automation, and seamless scalability, reducing administrative burden and improving operational efficiency. By moving away from siloed point products toward integrated zero-trust frameworks, organizations can streamline their security operations, reduce the resources required to manage access controls, and lower the risk of configuration errors that lead to vulnerabilities.
U.S. Zero Trust Network Access Market Trends
The U.S. zero trust network access market is projected to grow during the forecast period. The rapid expansion of third-party access and complex digital ecosystems across enterprises is driving market growth in the U.S. The U.S. organizations increasingly rely on external vendors, managed service providers, contractors, and technology partners to support core business operations. These third parties often require access to internal applications, development environments, or sensitive datasets, significantly increasing exposure if access is not tightly controlled. Traditional access models tend to grant broad network-level permissions, making it difficult to isolate and manage third-party risk effectively. Zero-trust architectures address this challenge by enabling application-level access that is strictly limited to what each third party needs, for only the required duration.
Asia Pacific Zero Trust Network Access Market Trends
The Asia Pacific zero trust network access industry is expected to be the fastest growing globally, at a projected CAGR of 26.2% over the forecast period. The expansion of digital services and online platforms across industries in APAC drives the ZTNA market, as enterprises increasingly deliver customer-facing applications and backend services that require secure remote access. Sectors such as banking, e-commerce, telecommunications, healthcare, and education rapidly deploy apps and portals to meet customer expectations for 24/7 accessibility and seamless online experiences. These digital services must be protected from unauthorized access, fraud, and abuse while still ensuring a smooth user experience. Legacy VPNs and perimeter defenses often introduce friction, latency, and security gaps that are unacceptable in high-velocity digital environments. This is especially important as APAC organizations pursue omnichannel strategies and integrate third-party APIs and services, which further expand the attack surface.
The zero trust network access industry in China is projected to grow during the forecast period. Another significant driver of ZTNA adoption in China is the rapid proliferation of mobile and remote connectivity, which has fundamentally reshaped how individuals and organizations interact with digital services. From urban centers to rural regions, employees routinely access corporate systems, SaaS platforms, and customer applications through a wide variety of devices and networks, many of which are outside traditional secure perimeters. This mobile-first environment complicates security governance and increases the risk of unauthorized access, especially when users connect from unsecured public networks or personal devices. Traditional perimeter defenses, such as Virtual Private Networks (VPNs), are not optimized for frequent mobility and often grant overly broad access, exposing internal systems to increased risk.
Europe Zero Trust Network Access Market Trends
The zero trust network access industry in Europe is expected to grow during the forecast period. The push toward digital sovereignty and greater control over access to sensitive data and systems is driving market growth. European enterprises are increasingly focused on maintaining control over who can access critical assets, where access originates, and under what conditions it is granted. This focus is driven by concerns over data protection, operational resilience, and dependency on external networks or providers. Traditional perimeter-based access models provide limited visibility and control once users are inside the network. Zero-trust frameworks provide detailed insight into access patterns and enforce strict policies based on identity and context. This enhances organizational control without limiting operational flexibility. As digital sovereignty becomes a strategic priority across Europe, ZTNA adoption is reinforced as a means of strengthening internal control over access governance.
The zero trust network access industry in the UK is anticipated to grow during the forecast period. A strong driver in the UK ZTNA market is the growing emphasis on protecting intellectual property and high-value digital assets. The UK is home to innovation-driven industries such as pharmaceuticals, aerospace, fintech, artificial intelligence, and advanced manufacturing, all of which rely heavily on proprietary data and research. Unauthorized access to these assets can result in severe competitive and financial losses, making security of access a strategic priority rather than a purely technical concern. Traditional network-based access controls often provide broader access than necessary, increasing the risk of internal misuse or accidental exposure. Zero-trust access enforces strict least-privilege policies, ensuring users can only access the specific applications and data required for their roles.
Key Zero Trust Network Access Company Insights
Some of the key companies operating in the market include Check Point Software Technologies Ltd. and Palo Alto Networks, among others.
-
Check Point Software Technologies Ltd. is a global cybersecurity company. Check Point delivers solutions designed to replace traditional perimeter-based security models with identity-centric, least-privilege access frameworks. Its ZTNA approach ensures that users, devices, and applications are continuously verified before access is granted, regardless of their location or network. By integrating strong identity authentication, device posture checks, and contextual access policies, Check Point enables secure remote access to private applications without exposing internal networks to the public internet. This model significantly reduces the attack surface while improving user experience for remote and hybrid work environments.
-
Cisco Systems, Inc. is a global technology company specializing in networking, cybersecurity, and digital communications. Cisco delivers an identity-driven security approach that moves enterprises beyond traditional perimeter-based access models. Its ZTNA capabilities focus on verifying user identity, device posture, and contextual risk before granting access to specific applications rather than entire networks. This ensures that access is granted on a least-privilege basis, reducing lateral movement and minimizing the attack surface in hybrid and remote work environments.
Menlo Security and Twingate are some of the emerging market participants in the zero trust network access industry.
-
Menlo Security is a cybersecurity company focused on protecting organizations from web-based threats through a cloud-native, isolation-driven security architecture. Menlo Security’s ZTNA capabilities are tightly integrated with secure web access and cloud security services, allowing enterprises to apply consistent security policies across private applications, SaaS platforms, and general web usage. Its architecture supports remote and hybrid workforces by delivering secure access through the cloud, eliminating the need for traditional VPNs that can introduce latency and security risks. Real-time monitoring, behavioral analytics, and policy-based controls provide visibility into user activity while maintaining performance and usability for end users.
-
Twingate is a modern cybersecurity company focused on delivering cloud-native, zero-trust secure access solutions. Twingate’s ZTNA platform integrates with common identity providers and endpoint security tools, enabling organizations to implement zero-trust policies without complex infrastructure changes. Its cloud-native design supports secure access across on-premises environments, public clouds, and hybrid deployments, making it well-suited for remote and mobile workforces. The platform emphasizes operational simplicity, offering centralized policy management, real-time visibility into access activity, and rapid deployment compared to legacy secure access technologies.
Key Zero Trust Network Access Companies:
The following key companies have been profiled for this study on the zero trust network access market.
- Akamai Technologies
- AppGate
- Check Point Software Technologies Ltd.
- Cisco Systems, Inc.
- Cloudflare, Inc.
- Fortinet, Inc.
- Menlo Security
- Netskope
- Nord Security
- Okta
- Omega Systems
- Palo Alto Networks
- Twingate
- Zero Networks
- Zscaler, Inc.
Recent Developments
-
In January 2026, Apono launched an integration with Check Point Software Technologies Ltd., introducing an advanced SASE-based Zero Standing Privilege architecture. The integration is designed to remove long-lived access permissions and enable real-time, just-in-time access across cloud environments. By minimizing persistent privileges, the solution helps organizations substantially reduce their attack surface while still preserving the flexibility and speed required by engineering teams, distributed workforces, and incident response operations.
-
In August 2025, Cloudflare, Inc. launched new capabilities in Cloudflare One, its Zero Trust platform, to enable organizations to securely adopt, develop, and deploy emerging generative AI applications. These enhancements allow enterprises to automatically gain visibility into how generative AI tools are being used across the organization, analyze usage patterns, and apply appropriate controls, helping teams boost productivity and innovation while maintaining strong security and privacy standards. As part of this update, Cloudflare has integrated AI Security Posture Management into its Zero Trust offering, addressing the risks associated with the rapid adoption of AI technologies and empowering businesses to scale AI usage with greater confidence and protection across all functions.
-
In September 2025, Akamai Technologies signed a strategic partnership with Seraphic Security to expand beyond the conventional security service edge (SSE) model for network access. This collaboration enables Akamai to deliver a simpler, more cost-effective approach that integrates seamlessly with broader security architectures. By embedding Seraphic’s secure enterprise browser into its Zero Trust Network Access (ZTNA) offering, Enterprise Application Access, Akamai strengthens its ability to provide an end-to-end security solution. As a result, customers gain comprehensive protection that effectively addresses traditional SSE use cases while improving usability and integration across the security stack.
Zero Trust Network Access Market Report Scope
Report Attribute
Details
Market size value in 2026
USD 2.42 billion
Revenue forecast in 2033
USD 11.03 billion
Growth rate
CAGR of 24.2% from 2026 to 2033
Actual data
2021 - 2025
Base Year
2025
Forecast period
2026 - 2033
Quantitative units
Revenue in USD million and CAGR from 2026 to 2033
Report coverage
Revenue forecast, company share, competitive landscape, growth factors, and trends
Segments covered
Component, deployment, enterprise size, application, end use, region
Regional scope
North America; Europe; Asia Pacific; Latin America; MEA
Country scope
U.S.; Canada; Mexico; UK; Germany; France; China; India; Japan; Australia; South Korea; Brazil; UAE; Saudi Arabia; South Africa
Key companies profiled
Akamai Technologies; AppGate; Check Point Software Technologies Ltd.; Cisco Systems, Inc.; Cloudflare, Inc.; Fortinet, Inc.; Menlo Security; Netskope; Nord Security; Okta; Omega Systems; Palo Alto Networks; Twingate; Zero Networks; Zscaler, Inc.
Customization scope
Free report customization (equivalent to 8 analysts working days) with purchase. Addition or alteration to country, regional & segment scope.
Pricing and purchase options
Avail customized purchase options to meet your exact research needs. Explore purchase options
Global Zero Trust Network Access Market Report Segmentation
This report forecasts revenue growth at global, regional, and country levels and provides an analysis of the latest industry trends in each of the sub-segments from 2021 to 2033. For this study, Grand View Research has segmented the zero trust network access market report based on component, deployment, enterprise size, application, end use, and region.
-
Component Outlook (Revenue, USD Billion, 2021 - 2033)
-
Solution
-
Services
-
-
Deployment Outlook (Revenue, USD Billion, 2021 - 2033)
-
Cloud
-
On-Premise
-
Hybrid
-
-
Enterprise Size Outlook (Revenue, USD Billion, 2021 - 2033)
-
Small & Medium Enterprises
-
Large Enterprises
-
-
Application Outlook (Revenue, USD Billion, 2021 - 2033)
-
Remote Access Security
-
Application Access Control
-
Secure Cloud Connectivity
-
Network Monitoring & Compliance
-
Others
-
-
End Use Outlook (Revenue, USD Billion, 2021 - 2033)
-
BFSI
-
IT and Telecommunications
-
Healthcare
-
Government & Defense
-
Retail & E-Commerce
-
Energy & Utilities
-
Education
-
Others
-
-
Regional Outlook (Revenue, USD Billion, 2021 - 2033)
-
North America
-
U.S.
-
Canada
-
Mexico
-
-
Europe
-
Germany
-
UK
-
France
-
-
Asia Pacific
-
China
-
India
-
Japan
-
South Korea
-
Australia
-
-
Latin America
-
Brazil
-
-
Middle East & Africa
-
UAE
-
Saudi Arabia
-
South Africa
-
-
Frequently Asked Questions About This Report
b. The global zero trust network access market size was estimated at USD 1.97 billion in 2025 and is expected to reach USD 2.42 billion in 2026.
b. The global zero trust network access market is expected to grow at a compound annual growth rate of 24.2% from 2026 to 2033 to reach USD 11.03 billion by 2033.
b. The hardware segment dominated the zero trust network access market with a market share of 54.9% in 2025. The rising integration of edge computing and localized data processing in industrial setups is further boosting the demand for hardware-based security.
b. Some key players operating in the market include Akamai Technologies, AppGate, Check Point Software Technologies Ltd., Cisco Systems, Inc., Cloudflare, Inc., Fortinet, Inc., Menlo Security, Netskope, Nord Security, Okta, Omega Systems, Palo Alto Networks, Twingate, Zero Networks, Zscaler, Inc.
b. Factors such as the rapid migration of applications to cloud and SaaS environments and rising frequency and sophistication of cyberattacks are the key factors driving the market growth.
Share this report with your colleague or friend.
Need a Tailored Report?
Customize this report to your needs — add regions, segments, or data points, with 20% free customization.

ISO 9001:2015 & 27001:2022 Certified
We are GDPR and CCPA compliant! Your transaction & personal information is safe and secure. For more details, please read our privacy policy.
Trusted market insights - try a free sample
See how our reports are structured and why industry leaders rely on Grand View Research. Get a free sample or ask us to tailor this report to your needs.